By
Raul Bernardino
Introduction:
Nowadays,
the complex global communications over the networks are need better tools to
monitor and manage them properly without a longer down time. This global
networks complexity, we can analog them as a simple control room in any hotels
for instance. Where in this control room can able monitor all movements around
the hotel and inside hotel building. The tools for monitoring the movement can
be used the CCTV, wire alarm control, anti theft alarm, general air conditioner
control and etc. The control monitors are helping the in-charge persons or on
duty officers to determine where the location of the defects or the troubles
are coming from. It asked an immediate action and followed guidance and steps that
are been agreed and written in the procedures in which is to minimize the
impacts. Rather than has to wait until it
becomes wider occurred impacts, in which it will be probably took more energy
and time to solve them.
With
this similar situation above is also applied to the network administration. We should
manage, control and monitor the deployment and maintenance of the hardware,
software and connection or data communication link over the networks.
According
to Saydam (1996), "Network management includes the deployment, integration and
coordination of the hardware, software, and human elements to monitor, test,
poll, configure, analyze, evaluate, and control the network and element
resources to meet the real-time, operational performance, and Quality of
Service requirements at a reasonable cost."
Even
it is a simple network such as it is consisting of several routers, hosts and
servers; we do still need to manage this network with a proper network
management tools. This is can help the network administrators. Several tools of
the network management that network administrator can use as follows:
- The interface failure detection at router or host or server: The appropriate network management tools, the network administrator may get report that one of the interface down. It is good detecting issue ahead and replaced that interface before it gets fail.
- The host monitoring: This can helps the network administrator to monitor all hosts in the network periodically.
- The traffic monitoring: This can helps the network administrator to monitor all the communication traffics over the network periodically and it is enable network administrator to drop unnecessary traffics (down-loader) or packages over the network as it needed.
- The rapid detection on routing table changes: This tool can help the network administrator to monitor the instability of the routing tables.
- The SLA Monitor: The service level agreement is a contract that both sides have agreed and the network administrator is based on whereas to monitor and to measure the performance of the service provider within the metrics.
- The intrusion detection: This tool can help the network administrator in which to monitor the strange traffic packages over routers or over networks.
There
are five area of network management model that international organization for
standardization defines as follows:
- Performance Management: The performance management is to measure and to maximize the utilization of the devices and services within network.
- Fault Management: The fault management is detecting and logs the issue including responding the fault condition of the network.
- Configuration Management: The configuration management is allowing the network administrator to track down and monitor all configurations of the devices and it is including the hardware and software.
- Accounting Management: The accounting management is allowing the network administrator to give the accesses to the users, logs the accesses of the resources over the network. The usages of the network resources are depending on the privileges.
- Security Management: The security management is controlling all the accesses base on the policies and procedures.
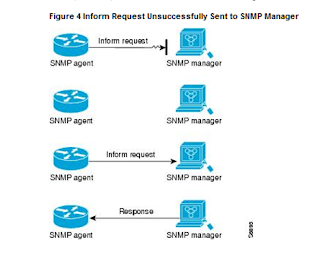
The network management infrastructure is managing the
devices in which contain of the objects of data (entities). Managing the network infrastructure as it
shows in the below diagram:
In conclusion:
The network management is important
in today’s global networks complexity. The network management tools is helping
to minimize the downtime or increasing the reliability of the networks whereas
it is also can be accessible from anywhere at any time.
References list:
1. Kurose, J.F. & Ross, K.W. (2010) Computer Networking: A Top-Down Approach.
5th ed. Boston:
Addison Wesley
2. University
of Liverpool/Laureate Online Education (2011) Lecture notes from Computer
Networking Module Seminar 8 [Online]. Available from: University of
Liverpool/Laureate Online Education VLE (Accessed: 24 September 2011)